API Security
We strongly recommend you make your Loqate integration as secure as possible, in order to keep your account safe and prevent any kind of malicious use. In this article we're going to talk about the various security options available to you, and some security best practices.
Security options
Loqate provides you with various security options, some of which can be applied across your whole account (and will therefore apply regardless of which services you're using) and others that can be applied to individual API keys (and therefore individual services). We recommend you apply as many of these as possible.
Securing your account
There are several features available to you in the Security section of your account, that apply across the whole of your account.
Some of these features are more or less suitable depending on the type of integration you use, whether it's client-side or server-side. For each one we've included a note regarding which integration type it's most suited to.
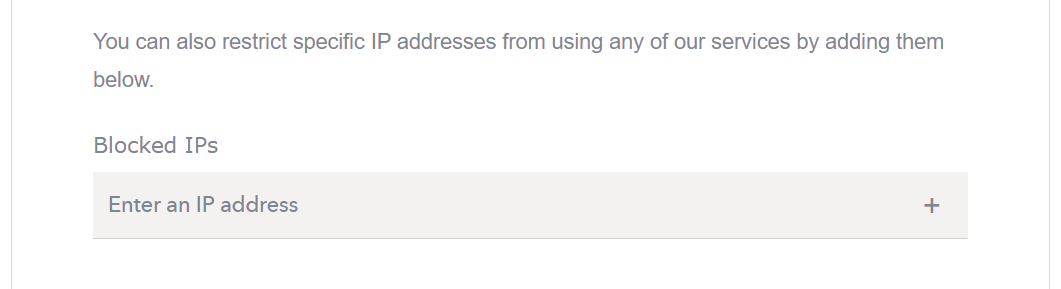
Restrict IP addresses
Use this feature to block one or more specific IP addresses, and ensure that they can't access any of your Loqate services.
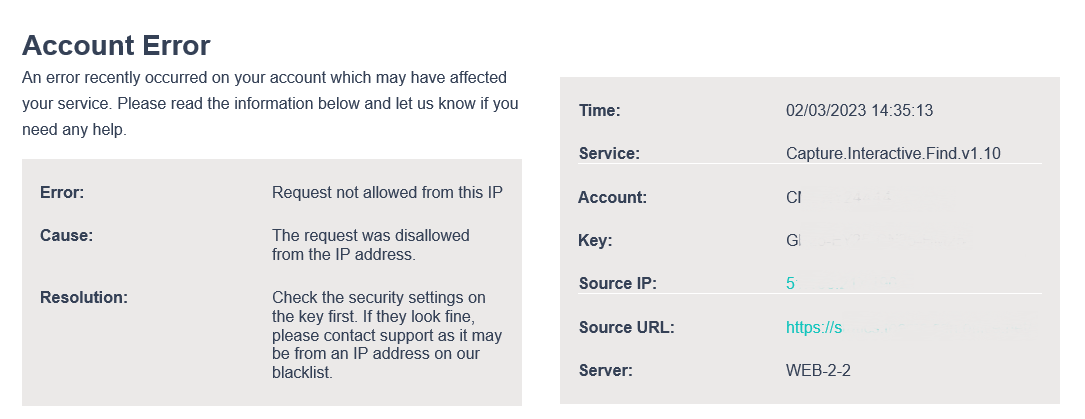
If someone then tries to access one of your services via a restricted IP address, you'll receive an email notification which contains details of the error that was generated, as well as information about which service was affected, what the source IP was, etc. Here's an example:

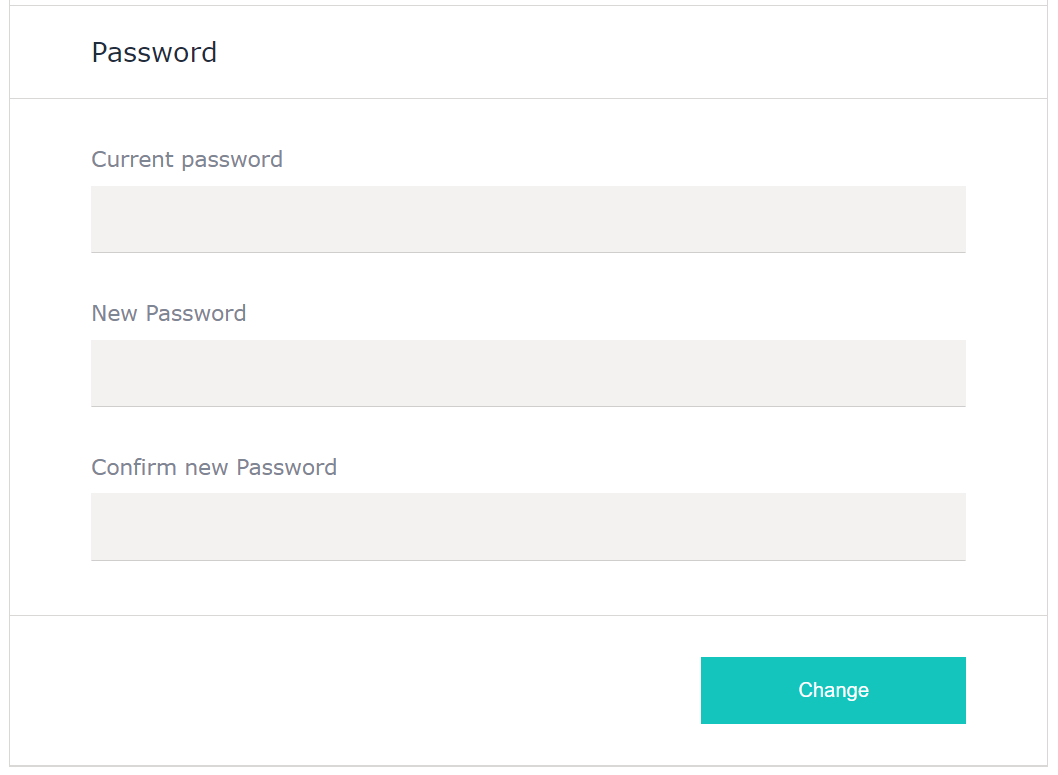
Account password
Make sure you use a strong password to prevent unauthorised access to your Loqate account.
Securing your API keys
All Loqate services authenticate your requests using the API key relevant to that request or service. In order to ensure your keys' security, we recommend that you:
- Restrict your keys to specific services (strongly recommended)
- Limit your keys by URLs or IP addresses
- Don't embed your keys anywhere that they could be extracted from
You can restrict and/or limit any key in the Your Services page of the Account section.
Select the key you want to edit, then click on the Limits tab where you'll see these options:
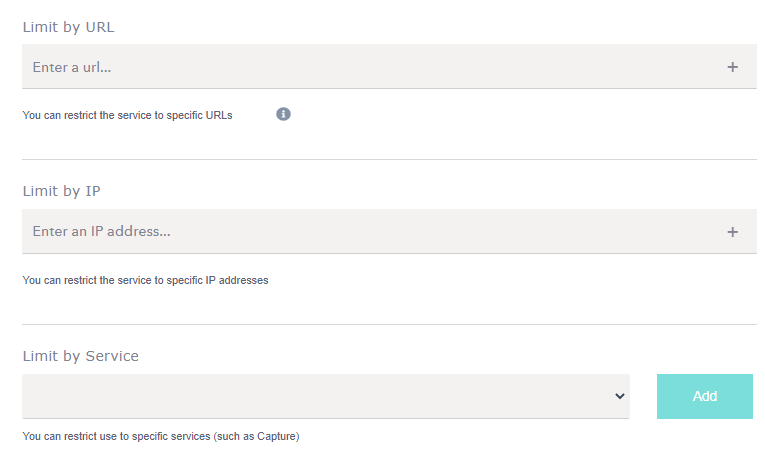
Limit by URL
To help prevent fraudulent or accidental use of one of your keys across domains, add the URLs that you expect the requests to be coming from. Enter a URL address you wish to limit in the text box and then click the plus icon. You can add as many URLs as you like.
You will also need to specify any subdomains and combinations of URLs that might be used. i.e. http://www.mysite.co.uk, http://www.mysite.com, https://mysite.co.uk, etc.

Limit by IP
Similar to the Daily Limit, this allows you to place request limits against a group of IP addresses, which should help manage your cashflow and cap individual usage. Enter an IP address you wish to limit in the text box and then click the plus icon. You can add as many IP addresses as you like.

Limit by Service
We strongly recommend you make use of this option, which allows you to restrict each API key to one or more Loqate services, rather than allowing each key to be used for any service.
The default value for this option is blank, in which case that key can be used for any Loqate service. You can select more than one service to limit an API key to, for example if you use the same key for Address, Email and Phone Validation.
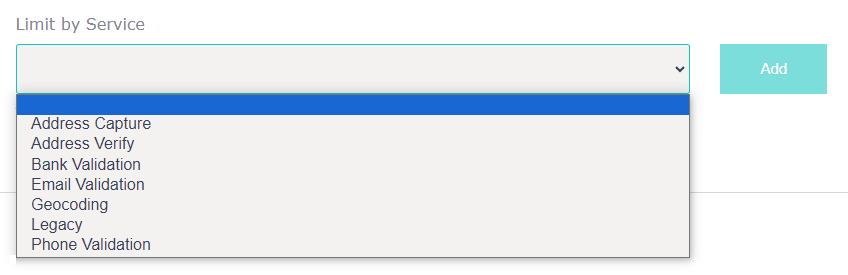
Each of those values represents a set of Loqate services. Here's how they're broken down:
- Address Capture
- Capture Find: https://api.addressy.com/Capture/Interactive/Find/
- Capture Retrieve: https://api.addressy.com/Capture/Interactive/Retrieve/
- Geolocation: https://api.addressy.com/Capture/Interactive/GeoLocation/
- Utilities: https://api.addressy.com/Capture/Interactive/Utilities/
- Legacy Capture products
- Address Verify
- Verify (International Batch Cleanse): https://api.addressy.com/Cleansing/International/Batch/
- Legacy Verify products including AddressCleansing, CleansePlus/Batch, CleansePlus/Interactive and Cleansing/International
- Bank Validation
- All Bank Validation APIs
- Email Validation
- All Email Validation APIs
- Phone Validation
- All Phone Validation APIs
- Geocode
- DistancesAndDirections
- Geocode: https://api.addressy.com/Geocoding/International/Geocode/
- All Geocoding APIs
- StoreFinder
- Find: https://api.addressy.com/StoreFinder/Interactive/FindPlaceNames/
- Retrieve: https://api.addressy.com/StoreFinder/Interactive/RetrieveCoordinates/
- All GovernmentData APIs
- Legacy
- A variety of legacy products including PostcodeAnywhereNorthAmerica, PostcodeAnywhereInternational and PostcodeAnywhere/Interactive
This list includes all currently-supported Loqate products. If you can't see a product you're using on this list, it's likely a legacy product and will be included either under Capture or Verify (if it's an older version of them) or the specific Legacy option. Please check with the Loqate Support team if you'd like to clarify which option to choose.
NOTE: if you created an Address Verification service via your Account section (i.e. following the instructions here), choose the Address Capture option rather than Address Verification (as this refers to the Verify product instead).

Integration options
There are two ways of integrating with Loqate's APIs - client-side and server-side - and it's worth considering the security implications of both when you're deciding how to integrate.
Both options provide access to the same services, and only require an API key.
- In a client-side integration all of the processing for an API in completed via a browser, on the end-user's device
- In a server-side integration all of the processing for an API is completed on a web server
We recommend you use a server-side integration to ensure the highest level of security, but in the following sections we'll explore the security implications of both options.
Client-side integrations
Client-side integrations are quick and easy to set up, and don't requite a large amount of technical expertise, so they give you the ability to get up and running without too much time or effort. The downside to this approach, however, is that it doesn't allow you to implement any of your own monitoring, which means you have less control over and visibility on the journey your customers go on.
From a security perspective they are also more vulnerable than server-side integrations, as they don't hide your API keys, which means your keys are visible to anyone viewing the source code of your website. We've put the previously-discussed security measures in place to help, including allow-listing features that let you specify which domains and IP addresses can use your API keys, but if you're a high-profile business, we recommend you use a server-side integration.
If you do decide to use a client-side integration, make sure you use the available measures to be as secure as you can. For instance, use the key-specific limits/restrictions mentioned earlier to lock your API keys down as much as possible.
Server-side integrations
Server-side integrations require more technical expertise and resources to set up, but offer you a greater degree of control over the user experience. Using this approach you have complete control over your monitoring, in terms of what your users are requesting and what they see in response.
This approach is also typically more secure, as it won't make any of your API keys visible, and as such we would always recommend this as the best option.
No API integration is invulnerable however, so we still recommend you use as many of the provided security options as possible even with a server-side integration.

Whichever approach you take to integrating with Loqate, make sure you consider the security implications and take steps to ensuring the security of your site.
If you have any further questions about API security, please get in touch with the Loqate support team.